 A new variant of SpyEye malware allows cybercriminals to monitor potential bank fraud victims by hijacking their Web cams and microphones, according to security researchers from Kaspersky Lab May 21. SpyEye is a computer trojan that specifically targets online banking users.
A new variant of SpyEye malware allows cybercriminals to monitor potential bank fraud victims by hijacking their Web cams and microphones, according to security researchers from Kaspersky Lab May 21. SpyEye is a computer trojan that specifically targets online banking users.
Like its older cousin, Zeus, SpyEye is no longer being developed by its original author but is still widely used by cybercriminals. SpyEye’s plug-in-based architecture allows third-party malware developers to extend its original functionality, a Kaspersky Lab malware researcher said.
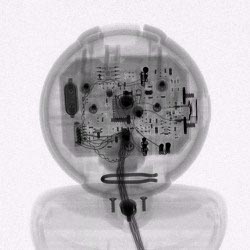
This is exactly what happened with the new Web cam and microphone spying feature, implemented as a SpyEye plug-in called flashcamcontrol.dll, he said. As suggested by the DLL’s name, the malware accesses the two computer peripherals by leveraging Flash Player, which has Web cam and microphone control functionality built in.
Under normal circumstances, users get prompted to manually allow Web sites to control their computers’ Web cam and microphone via Flash. However, the SpyEye plug-in silently whitelists a list of online banking Web sites by directly modifying Flash Player configuration files.
At first, the Kaspersky Lab researchers thought that this might be part of a scheme to bypass facial recognition systems used by some banks for secure authentication. However, after contacting the targeted organizations, they learned that none of them had any webcam-reliant features on their websites.
The Kaspersky researchers later found out, by analyzing a different SpyEye component, that the malware injects the webcam and microphone hijacking Flash content into the targeted online banking websites locally, when these sites are opened in a browser on the infected computers.
Both webcams and microphones can be disabled from the operating system, either manually or with the help of specialized software, but that would hardly be convenient, especially for people who regularly use these peripherals. It's much easier to prevent the infection in the first place by following basic security best practices like keeping all computer software up to date, running an up-to-date antivirus program, scrutinizing links before clicking on them and avoiding installing programs from suspicious sources.